Security reports, verified for
engineers
Receive verified security reports from Triage's researcher community. Triage confirms what's real and sends proof to engineers.
Feb 24
Submitted 2026
7.1
High
CWE-639
Weakness
Tri's Report
Executive Summary
An Insecure Direct Object Reference (IDOR) vulnerability has been identified in the portfolio API endpoint of the Super Secure Crypto application at /api/v2/user/portfolio. An authenticated user can access any other user's portfolio holdings, transaction history, and linked wallet addresses by enumerating the account_id parameter in GET requests without proper authorization checks.
Recommended Fix
Implement server-side authorization checks to verify that the authenticated user's session token corresponds to the requested account_id before returning any data. Replace sequential integer IDs with UUIDs and add rate limiting.
Get discovered by top researchers.
Triage Security is where security researchers go to find bug bounty and vulnerability disclosure programs. Add yours today and stand alongside these industry leaders.
Triage in minutes, not weeks.
Traditional bug bounty platforms leave reports sitting in a queue for days or weeks, waiting for a human triager to get around to them. With Tri, our AI triage agent, every incoming report is analyzed the moment it arrives. Automatically assessing severity, verifying scope, checking for duplicates, and asking smart follow-up questions automatically. Your team gets actionable, triaged reports instead of a growing backlog.
Faster fixes. Lower costs. Zero backlog.
Evidence backed triage.
Tri spins up an isolated environment, follows the researcher's reproduction steps, and captures a complete evidence pack: screenshots, payloads, HTTP traces, and reproduction notes your developers can act on immediately. Unsupported or flaky cases are labeled clearly and routed to human review, so your team only sees reports worth fixing. When it's time to justify a bounty payout, the evidence is already there, documented and exportable.
Fix faster. Justify payouts. Ship with confidence.
Triage Evidence
1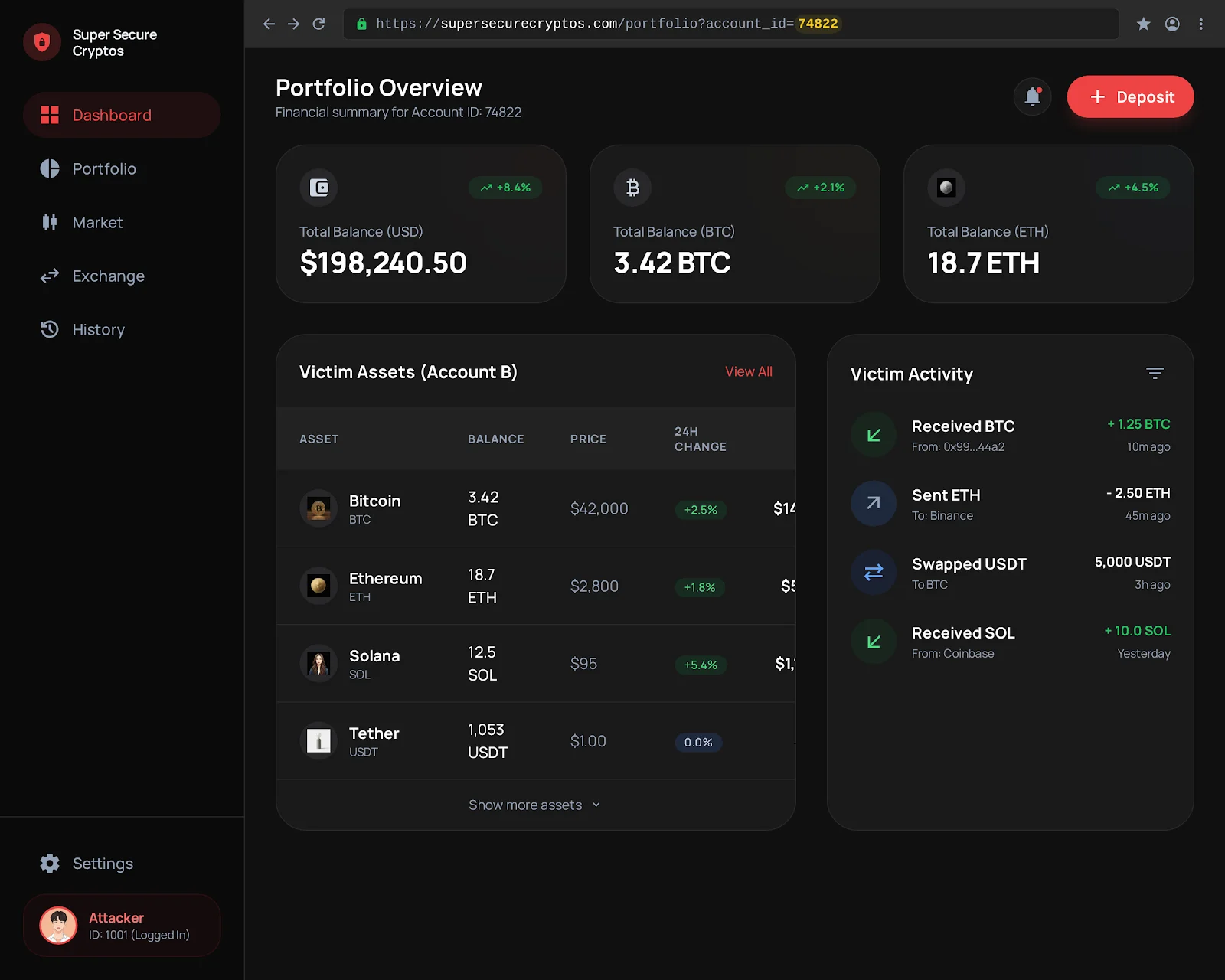
2a1b1b63
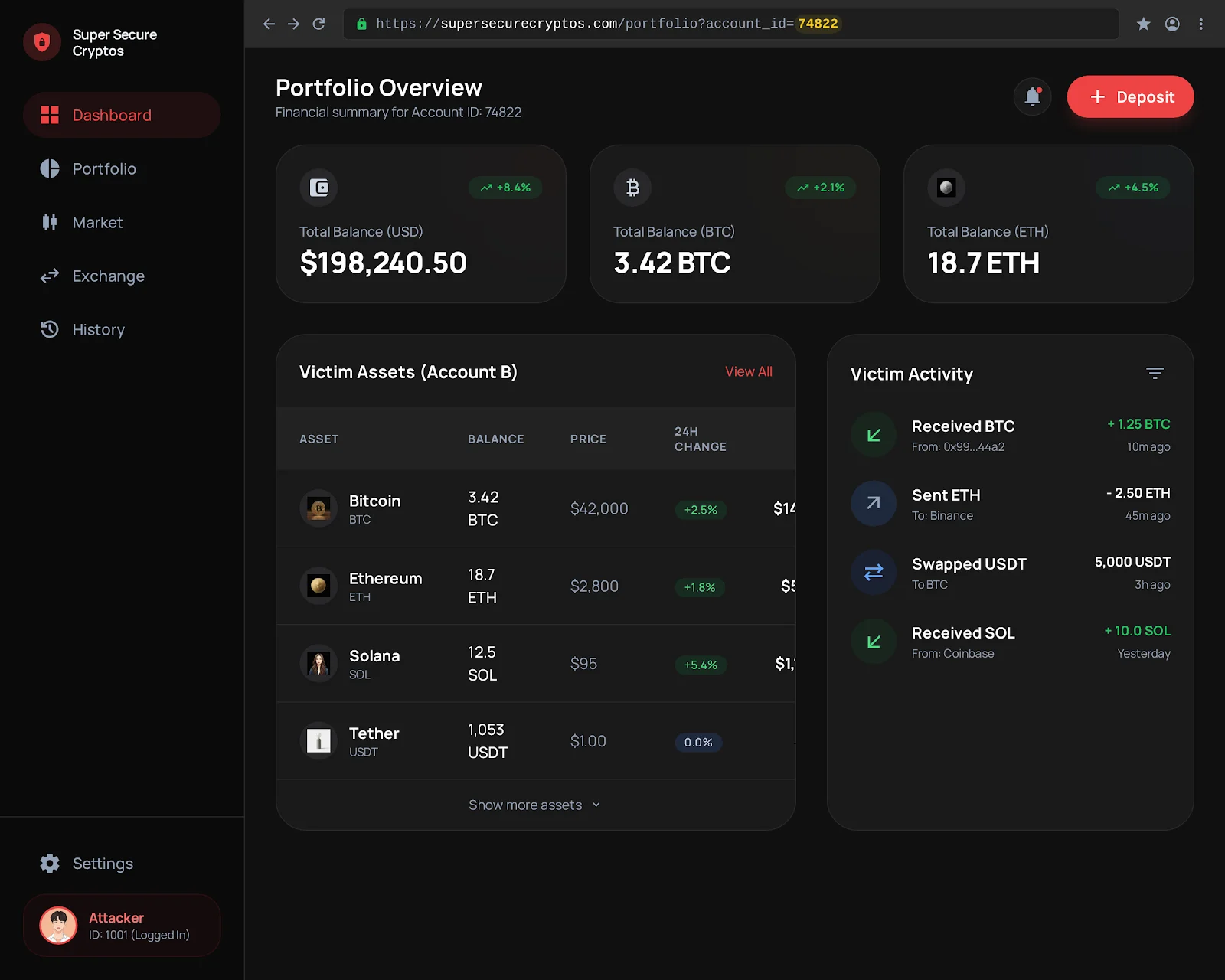
A screenshot of the victim's portfolio dashboard accessed via account_id=74822, showing full financial summary, asset balances (3.42 BTC, 18.7 ETH, 12.5 SOL, 1,053 USDT), and transaction activity while logged in as the attacker (ID: 1001).
All Files
7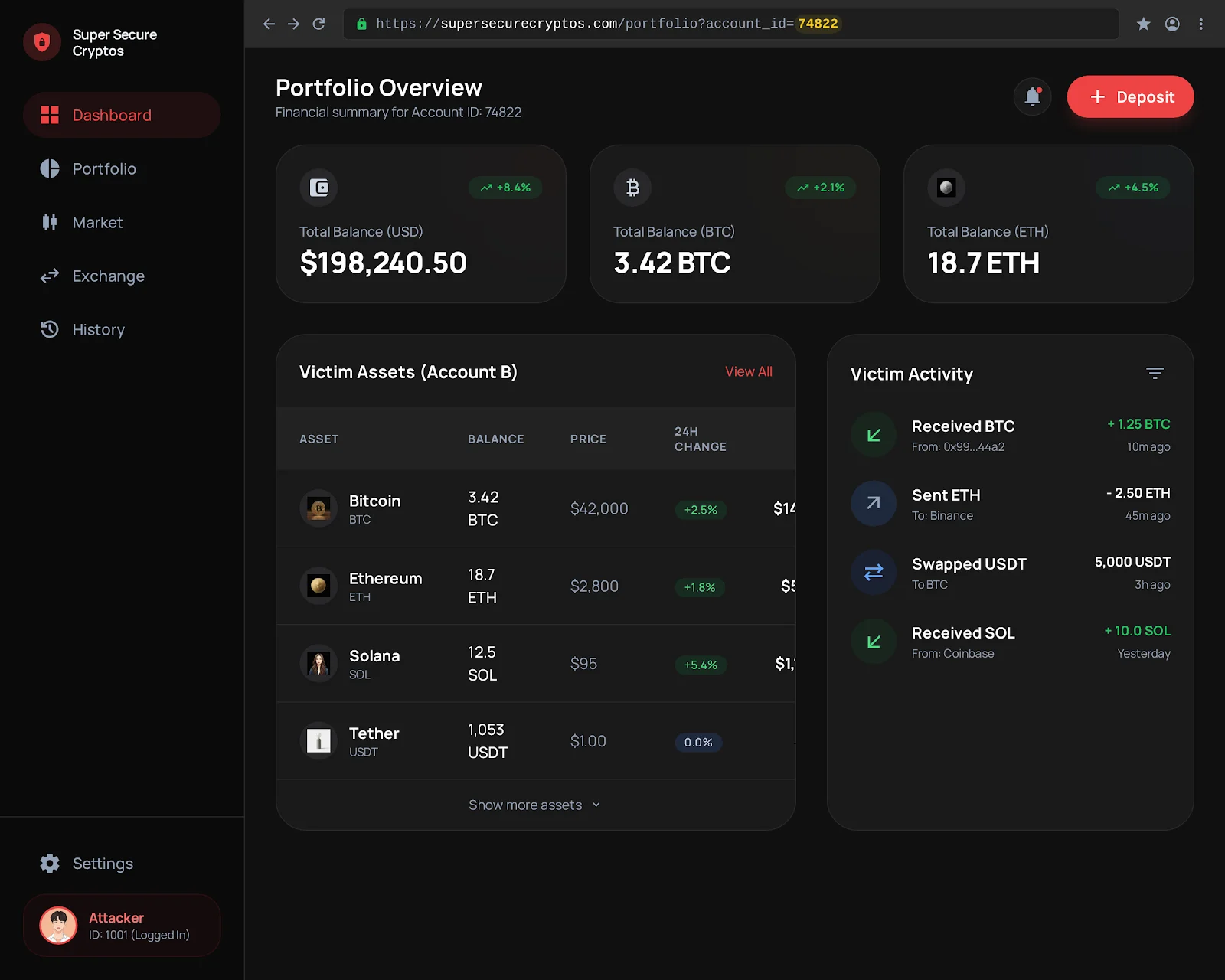
Connects with your stack.
Triaged reports flow directly into the tools your team already uses. No copy-pasting, no context switching. When Tri finishes triage, actionable tickets land in Jira or GitHub and notifications hit Slack.
Your workflow. Our automation. Zero friction.
Audit evidence, generated automatically.
Don't worry when auditors ask for Common Criteria 7.1 or ISO 27001 artifacts. Triage generates compliance-ready reports on your behalf with vulnerability summaries, remediation timelines, triage decisions, and evidence packs. All exportable and audit-ready from day one.
Compliance without the busywork.
Submit Report
Describe the vulnerability
What asset(s) are affected? What is the vulnerability? In clear steps, how do you reproduce it?
Summary:
The platform's portfolio API endpoint (/api/v2/user/portfolio) is vulnerable to an Insecure Direct Object Reference (IDOR) via the account_id parameter. An authenticated user can access any other user's portfolio holdings and linked wallet addresses by enumerating the ID value.
Your brand, your program.
Your vulnerability disclosure program should feel like yours. Triage lets you fully customize the researcher facing experience. Upload your logo, set your brand colors, and choose between dark and light mode. Embed the submission form directly on your site with an iframe, point a custom domain like security.yourcompany.com, or let researchers discover you through the Triage public directory. Every surface carries your identity.
One platform, every surface, fully branded.
What makes Triage Security unique.
Built for teams of every size, and the most researcher-friendly platform in the industry.
Spam Reduction
Advanced bot fingerprinting and spam filtering. You only see valid vulnerabilities.
Invite Only
Start with high-signal researchers, or bring your own community before going public. You control who has access and when.
Built For Everyone
Start without a sales call. Get up to 400 triages included for free with your plan. Need more? Pay per usage, not capacity or seats.
Global
We're less restrictive than other platforms so you can access top-tier talent worldwide. We handle compliance and payouts on your behalf.
Launch in 30 minutes.
Start small. Scale verification when you're ready.
Connect Domain
Link your domain and configure DNS so your program lives at a URL you control.
Define Scope
Specify which assets, endpoints, and vulnerability types are in scope for researchers.
Review Program
Preview your program page, adjust reward tiers, and finalize your policies before going live.
Launch as Bug Bounty or VDP
Go live with a paid bug bounty or a free vulnerability disclosure program. Switch anytime.
Connect your custom domain (Optional)
Get a custom domain like security.yourdomain.com that links to your program page.
How much are you spending on triage?
Compare annual platform costs as submissions scale.